Breaking My Little Pony: Frequency Analysis for Breaking Ciphers | by Jonathan Keller | Towards Data Science

inch ✌🏻 on Twitter: "I typed zjylht into a caesar cipher decoder and scream is one of the results. I guess we're on the right track?… "
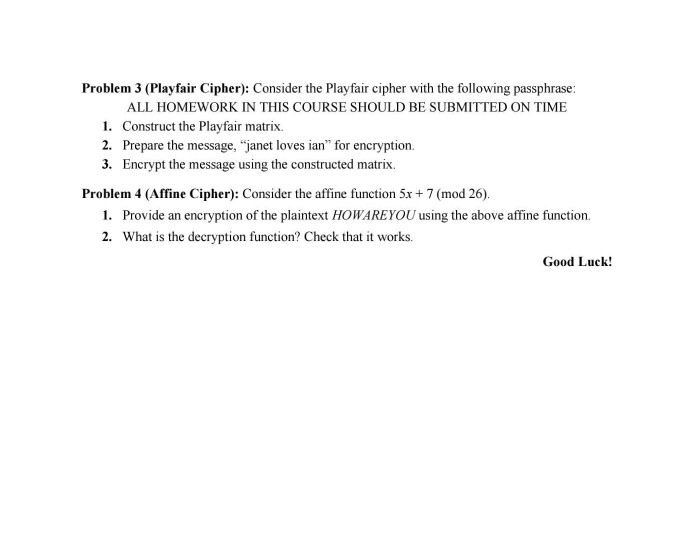
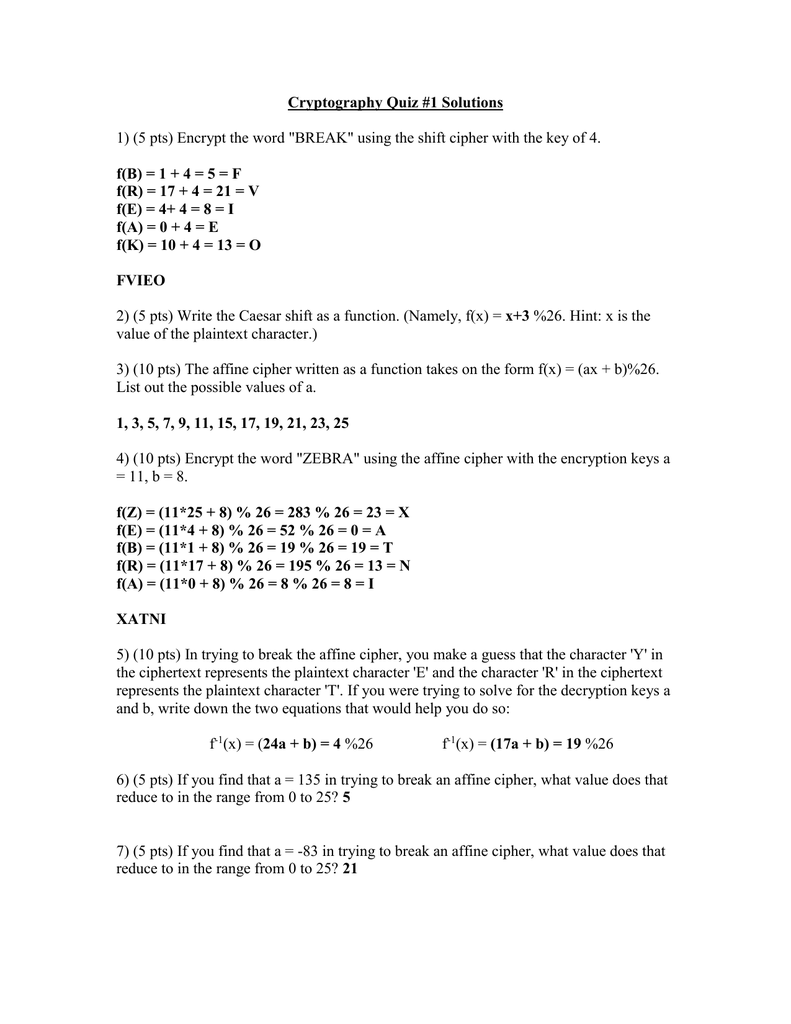
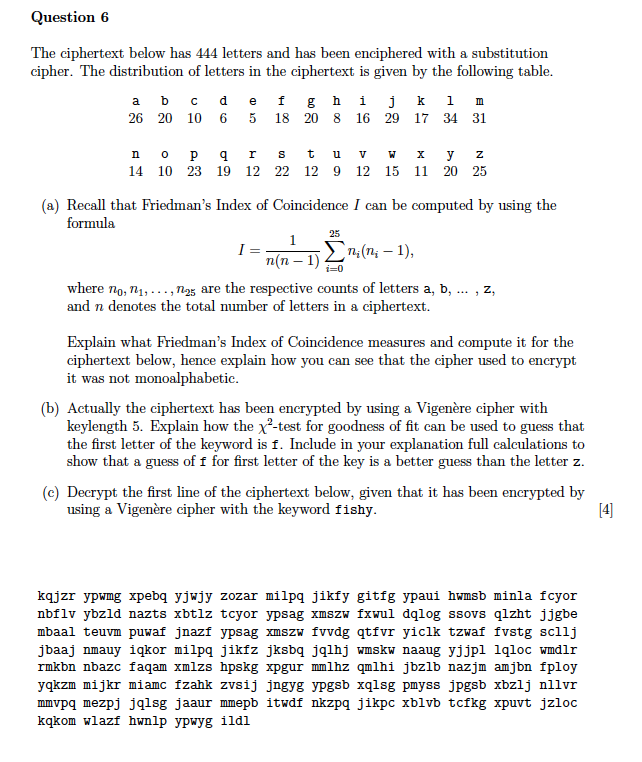
Homework 1: Due Friday by 4:30 pm. Instructions – show work and clearly explain your solution path. You may use a computer pr

![PDF] An Improved Guess-and-Determine Attack on the A5/1 Stream Cipher | Semantic Scholar PDF] An Improved Guess-and-Determine Attack on the A5/1 Stream Cipher | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/adf3978659c103dc700f1db3826714ca8098d0e5/2-Figure1-1.png)




.png)